
The 2.4GHz band has been a staple for tech devices ever since the first Wi-Fi networks were established back in 1997. While this frequency has been extremely helpful, thanks to its lack of licensing, the mass use of this band also comes with numerous drawbacks, including reliability and bandwidth challenges. Why has 2.4GHz been immensely popular amongst devices, what challenges does it face, and what technologies could engineers look towards?
Top Stories This Week
- 2.4GHz vs 5GHz vs 6GHz: Understanding The Future Of Wi-Fi Frequencies
- Ex-Apple Engineer Flees To China After Allegedly Stealing Autonomous Car Tech Data
- Underwater Surveillance: Finland’s Solution To Infrastructure Vulnerability
- UK Launches First Full-Sized Autonomous Bus Service With Top Speed Of 50 Miles Per Hour
- Samsung Electronics, Tesla Heads Meet To Discuss Cooperation In High-Tech
- New Side-Channel Attack On ARM: Implications For IoT Security
- Meta Pulls The Curtain Back On Its A.I. Chips For The First Time
- Apple Wearable Tags Described In Disguised Patent Application
- Wearable Can Take Multiple Sweat Samples
- Novel 3D Printing Method A ‘Game Changer’ For Discovery, Manufacturing Of New Materials
- Industrial Robot Gets Open-Source Upgrade
Hardware Business News
Ex-Apple Engineer Flees To China After Allegedly Stealing Autonomous Car Tech Data

The U.S. Department of Justice has taken legal action against a former Apple software engineer, Weibao Wang, accusing him of engaging in the theft or attempted theft of technology for a period of at least four months before he resigned from the company. According to the indictment, Wang allegedly shared Apple’s valuable information with an unidentified Chinese company involved in developing self-driving cars, raising concerns about protecting intellectual property and potential national security implications. How could a former Apple employee with broad access to company databases exploit their position to steal sensitive technology without detection potentially? What are the potential consequences for Apple and the broader technology industry when trade secrets are compromised and transferred to foreign entities? What steps can technology companies and government agencies take to enhance security measures and prevent the unauthorised transfer of critical technology?
Underwater Surveillance: Finland’s Solution To Infrastructure Vulnerability

The development of underwater infrastructure has a rich history spanning over a century, with advancements in technology enabling the laying of cables for communication and power across vast oceans. However, these underwater networks face numerous challenges, including corrosion, wildlife interference, and the potential for deliberate sabotage. Recent incidents near the shores of the UK and Denmark have highlighted the vulnerability of such infrastructure to hostile attacks, emphasising the need for enhanced security measures. In response, Finnish engineers have introduced an advanced underwater surveillance system, UNWAS, designed to protect crucial infrastructure such as power cables and internet connections. This article explores the history and challenges of underwater infrastructure, the innovations brought by Finnish engineers, and the potential impact of surveillance systems on the future of infrastructure protection.
UK Launches First Full-Sized Autonomous Bus Service With Top Speed Of 50 Miles Per Hour

The United Kingdom has achieved a remarkable milestone in the autonomous transportation sector with the launch of its first full-sized autonomous bus service, known as AB1. Connecting the Ferrytoll Park and Ride in Fife with the Edinburgh Park Transport Interchange in Scotland, the AB1 service covers a 14-mile route, including the iconic Forth Road Bridge. This pioneering trial, part of the CAVForth project, employs five autonomous buses with advanced sensors and AI. How does the launch of the AB1 autonomous bus service signify a milestone for the autonomous technology sector in the U.K.? What are the key features of the AB1 service, including its route, passenger capacity, and ticket pricing? How is the consortium of partners involved in the project, and what are the expectations for the future of autonomous driving in public transportation based on comments from industry experts?
Samsung Electronics, Tesla Heads Meet To Discuss Cooperation In High-Tech

Tesla CEO Elon Musk and key executives met with Samsung Electronics Chairman Lee Jae-Yong and representatives on May 14, 2023, to explore potential cooperation in next-generation technology for fully autonomous driving. As the world’s leading chipmaker, Samsung’s meeting with Tesla signifies the convergence of advanced driver-assist systems and chip manufacturing expertise. While the companies have been co-developing self-driving chips since 2019, this meeting aims to strengthen their partnership further and propel the technology forward. With Tesla eyeing Taiwan Semiconductor Manufacturing Co. as an option, Samsung aims to secure Tesla’s commitment and ramp up chip production. What areas of collaboration are Tesla and Samsung exploring for next-generation technology in fully autonomous driving? How does the meeting between Elon Musk and Chairman Lee Jae-Yong indicate an intention to enhance the existing partnership and take autonomous driving technology to the next level? What are the implications for Tesla in ensuring Samsung’s increased chip production, considering the chip shortage challenges faced by the global auto industry?
Hardware Engineering News
New Side-Channel Attack On ARM: Implications For IoT Security

Researchers recently unveiled a new side-channel attack against ARM TrustZone, a security feature used in computer chips, during the Black Hat Asia conference. Although ARM claims that the attack poses minimal threat to current ARM cores, the implications for IoT security are significant. With billions of IoT devices relying heavily on ARM processors, the potential repercussions are concerning. What are side-channel attacks, and why are they challenging to defend against compared to traditional hacking methods? How did the researchers demonstrate a side-channel attack on ARM TrustZone, and what does this reveal about the security vulnerabilities of IoT devices? What measures can software and hardware engineers adopt to mitigate the risk of side-channel attacks, and how can the IoT industry prioritise security in the face of evolving threats?
Meta Pulls The Curtain Back On Its A.I. Chips For The First Time

Meta, the social networking giant formerly known as Facebook, has disclosed its internal silicon chip project for the first time. The company showcased custom chips designed to enhance artificial intelligence (AI) tasks and video processing. One of the chips, the Meta Scalable Video Processor (MSVP), optimises video processing while reducing energy consumption, while the other chip, the Meta Training and Inference Accelerator (MTIA), aids in AI-specific tasks, particularly inference. What motivated Meta to invest in custom computer chips for AI and video processing? How do the Meta Scalable Video Processor (MSVP) and Meta Training and Inference Accelerator (MTIA) chips contribute to improving video processing and AI tasks, respectively? Finally, in what ways could Meta’s custom chips influence the development of the metaverse, virtual reality, augmented reality, and generative AI?
Apple Wearable Tags Described In Disguised Patent Application

Apple’s patent application for wearable tags has recently surfaced, shedding light on the company’s plans for health and sports-related functions. It is believed that these tags will be worn on the body or attached to clothing, offering a range of capabilities such as posture monitoring, sun exposure tracking, physical therapy assistance, fall detection, fitness tracking, and more. The application was initially filed in 2020 under the names of Apple engineers, but now that it has been published, Apple is listed as the official applicant. While the Apple Watch already offers fitness tracking features, these wearable tags may provide more detailed analysis for activities like running, golf swings, and tennis strokes. This article explores the potential implications of Apple’s wearable tags.
Hardware R&D News
Wearable Can Take Multiple Sweat Samples

Researchers at the University of Hawaii at Manoa has developed a ground-breaking wearable device called the “sweatainer” that revolutionises sweat analysis. Unlike traditional methods, the sweatainer employs a complex microfluidic architecture created through 3D printing, allowing for multiple sweat samples to be collected over time and stored separately for later analysis. This innovative technology has the potential to provide valuable insights into various health conditions and routine issues, offering non-invasive and convenient sampling. The device also supports onboard colourimetric biomarker analysis, eliminating the need for sophisticated laboratory equipment. How does the use of 3D printing enable the creation of a complex microfluidic architecture within the sweatainer? What specific health conditions and routine issues can be effectively monitored and assessed through the collection and analysis of sweat biomarkers using this wearable device? How does the incorporation of onboard colorimetric biomarker analysis simplify the process and make the sweatainer more accessible for both healthcare professionals and individuals monitoring their own health?
Novel 3D Printing Method A ‘Game Changer’ For Discovery, Manufacturing Of New Materials
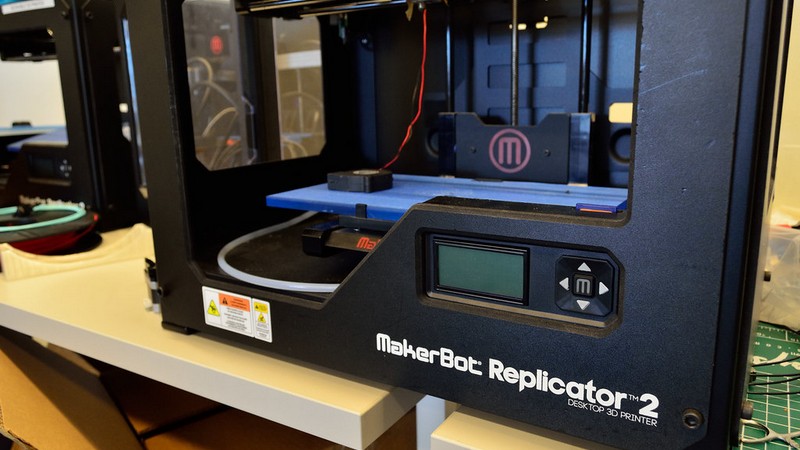
A groundbreaking 3D printing method developed by Yanliang Zhang, associate professor at the University of Notre Dame, is poised to revolutionise materials discovery and manufacturing. The high-throughput combinatorial printing (HTCP) technique allows for producing materials with gradient compositions and properties at microscale resolution, surpassing the capabilities of conventional manufacturing processes. By mixing multiple aerosolised nanomaterial inks in a single printing nozzle and dynamically adjusting the ink mixing ratio during printing, Zhang’s method accelerates materials discovery to an unprecedented scale. How does the high-throughput combinatorial printing (HTCP) method differ from conventional manufacturing? How can the versatility of HTCP contribute to advancements in fields such as energy harvesting and biomedical applications? What role will machine learning and artificial intelligence play in leveraging the data-rich nature of HTCP to accelerate the discovery and development of new materials?
Open-Source Hardware News
Industrial Robot Gets Open-Source Upgrade

Industrial robots, known for their exorbitant price tags, become surprisingly affordable once they reach the end of their life cycle. [Excessive Overkill] delves into this topic, sharing insights in a video where he acquires a discarded robot and attempts to revive it. By scavenging for spare parts, installing open-source firmware, utilising LinuxCNC, and Mesa FPGA cards, the robot is given a new lease on life. While challenges such as sourcing firmware upgrades and resolving servo control issues persist, the project showcases the possibilities of repurposing industrial-grade machines. What are the main challenges faced when reviving an industrial robot? How does the adoption of open-source firmware and alternative controllers contribute to extending the usability of scrapped robots? Apart from repurposing old robots, what other benefits can be gained from building open-source controllers, particularly regarding security and customisation?


